Paragon Solutions Executive Accidentally Exposes Spyware Control Panel in LinkedIn Photo
Israeli surveillance firm’s “epic OPSEC fail” reveals dashboard of secretive Graphite spyware platform
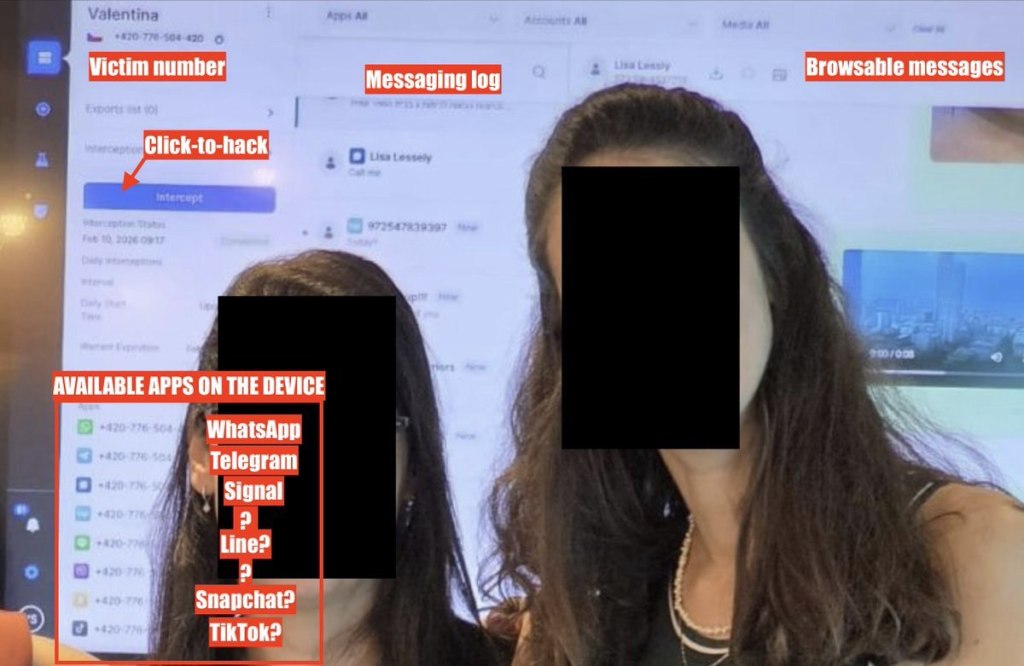
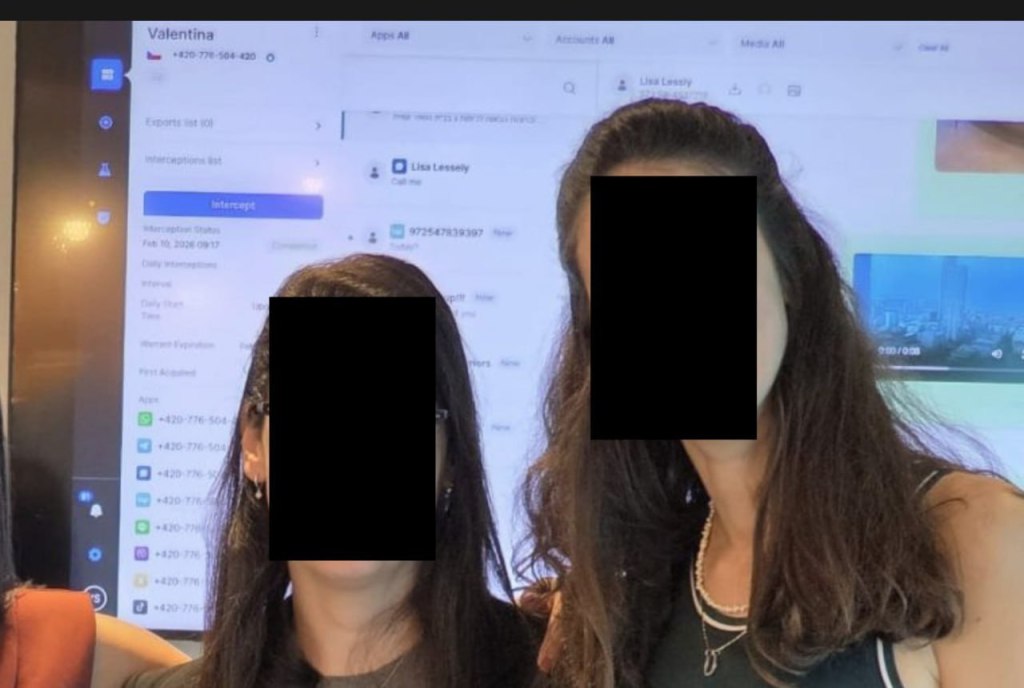
Reut Yamen, General Counsel and Chief Compliance Officer at Israeli spyware firm Paragon Solutions, inadvertently exposed the company’s secretive Graphite surveillance platform after posting a photo to LinkedIn on February 11, 2026. The image, which showed Yamen and a colleague posing in front of a large screen displaying what appears to be an operational control panel, was quickly deleted—but not before it had been captured and circulated online.
Cybersecurity researcher Jurre van Bergen first spotted the post and shared it publicly. John Scott-Railton, a senior researcher at the University of Toronto’s Citizen Lab, described the incident as an “epic OPSEC fail.”
What the leaked image revealed
The screenshot visible in the photo displayed a dashboard interface containing:
- A Czech phone number (+420-776-504-420) with a target labeled “Valentina”
- Active interception logs dated February 10, 2026
- An “Intercept” button for initiating surveillance
- Interfaces for monitoring encrypted messaging applications including WhatsApp
- Categories for browsing apps, accounts, and media on the target device
- A list of phone numbers apparently extracted from various messaging platforms
Security researchers who analyzed the image identified icons suggesting the platform can access multiple encrypted messaging services, including WhatsApp, Telegram, and Signal, among others.
Some researchers have noted that the dashboard may represent a demo or testing environment rather than active surveillance operations, though this has not been confirmed.
What is Graphite?
Graphite is Paragon Solutions’ flagship spyware product, classified by researchers as “mercenary spyware”—sophisticated surveillance software sold to government clients. According to technical analyses by Citizen Lab:
- The software uses “zero-click” exploits to compromise devices without requiring any action from the target
- Once installed, it can extract messages from encrypted applications before encryption or after decryption
- Operators can access stored data, activate microphones and cameras, and monitor communications in real-time
- Forensic researchers have identified artifacts labeled “BIGPRETZEL” on infected Android devices
Founded in 2019 by veterans of Israeli intelligence services, Paragon has positioned Graphite as a more ethically operated alternative to NSO Group’s Pegasus spyware. The company maintains it sells only to vetted democratic governments.
Previous controversies
WhatsApp targeting (January 2025): Meta notified approximately 90 users across multiple countries that their devices had been targeted by Paragon’s spyware. Victims reportedly included journalists and civil society members, prompting WhatsApp to send Paragon a cease-and-desist letter.
Italian journalists targeted: Among those notified was Francesco Cancellato, editor-in-chief of Italian investigative outlet Fanpage.it, known for critical coverage of Prime Minister Giorgia Meloni’s party. The Italian government launched an investigation, and Paragon reportedly terminated its contract with Italy following the scandal.
Citizen Lab findings (June 2025): Researchers confirmed with “high confidence” that two journalists were targeted using Graphite, including Italian journalist Ciro Pellegrino. Apple subsequently patched the underlying vulnerability in iOS 18.3.1 (CVE-2025-43200).
U.S. government use: In January 2025, the Trump administration publicly acknowledged that U.S. Immigration and Customs Enforcement (ICE) had purchased Graphite for enforcement operations.
Known government clients
According to Citizen Lab analysis, Paragon’s clients include government agencies in Australia, Canada, Cyprus, Denmark, Israel, and Singapore. Civil rights groups have documented Graphite deployments in Canada, including by Ontario Provincial Police, raising concerns over surveillance of activists.
Paragon was reportedly acquired by U.S.-based private equity firm AE Industrial Partners in late 2024 in a deal valued at approximately $500 million. Former Israeli Prime Minister Ehud Barak, an early investor, reportedly received $10-15 million from the transaction.
Industry implications
The accidental disclosure highlights the operational security challenges facing the commercial spyware industry—an industry built on secrecy that has faced increasing scrutiny from researchers, journalists, and regulators.
“Commercial spyware makers will inevitably face abuse of their products once they start selling to a broader customer base,” Scott-Railton told reporters. “It’s not just dictatorships that abuse spyware—it happens in democracies too.”
The irony that Paragon’s chief compliance officer—the executive responsible for ensuring the company follows security protocols—was the source of the leak has not been lost on observers.
Sources: Citizen Lab, Cybersecurity News, The Hacker Wire, Reuters, original social media posts by Jurre van Bergen and John Scott-Railton